A hash is a one way function that transforms a string of data of arbitrary size to a bit string of a fixed size. This function has the following properties:
- It is quick
- It is impossible to figure out the original string of data from the hash. (except by brute force, trying all possible input strings until we obtain the same hash)
- Two different inputs will always produce different outputs
- A small change to the input string changes the output radically
- Same input always produces same output.
Hash is useful for example when you want to make sure that a file that you have downloaded is the file that the owner of the file intended for you to download and it has not been modified in transit.
For example, you want to download notepad++ so you go to the website and click on the link to download the Notepad++ Installer. A file downloads, but, how do you know the file hasn’t been corrupted or somehow modified while downloading?
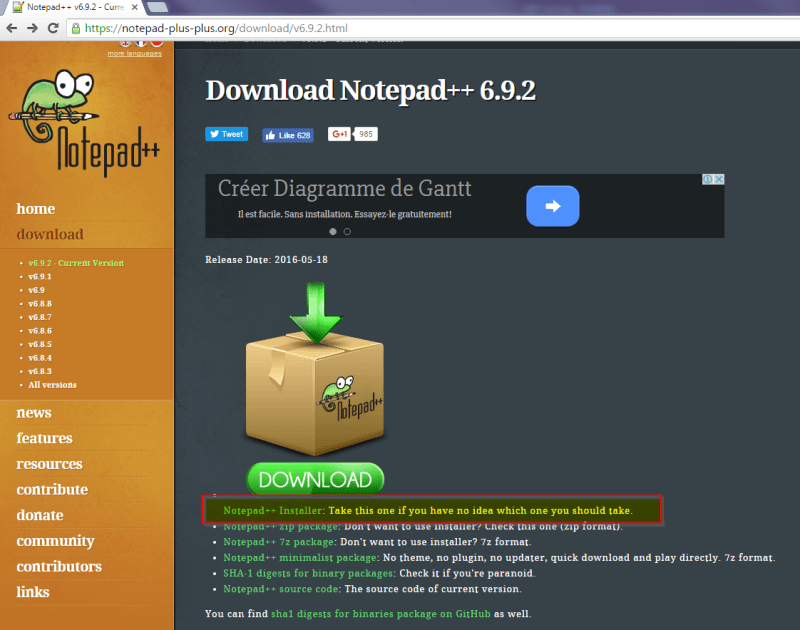
You can check if the hash of the file you downloaded is the same hash that the owner of the website indicates. If you click on the link called “Sha-1 digests for binary packages”
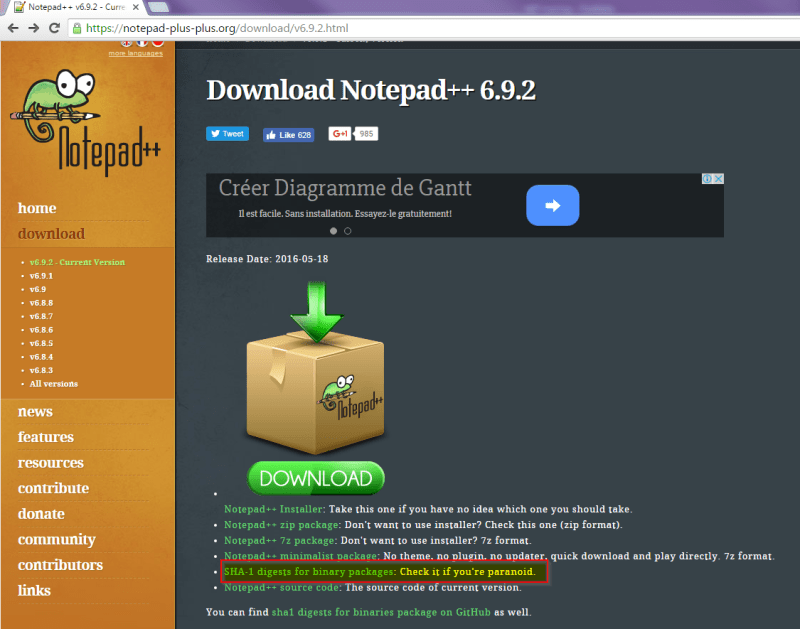
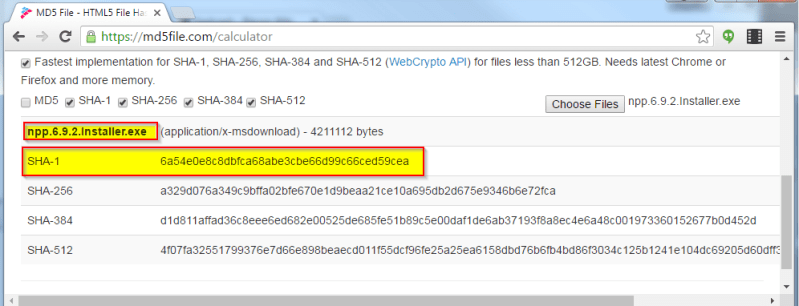
You can see the SHA-1 hash (there are many hash functions, SHA-1, MD5, SHA-256…) of the file should be 6a54e0e8c8dbfca68abe3cbe66d99c66ced59cea
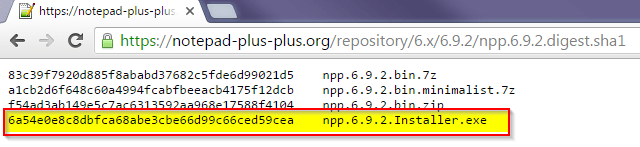
You can now use any SHA-1 hash calculator to chech that the file you have downloaded matches the hash that should be. This would indicate that the bits of this file are exactly the same bits as of the file that the website owner put on the website for download. If we change even 1 bit, the hash would be completely different.
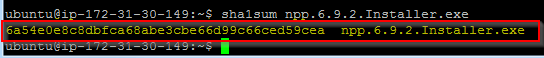
If you have a linux computer you can use command sha1sum and you can see that the resulting hash is exactly the same one. You don’t need to go character by character checking, since if the file had been altered, the result would be wildly different.
If you don’t have a linux command line you can use an online sha1 calculator to see that with the same input, the SHA-1 function will return the same hash, no matter in which platform or computer you execute the function.
Hash functions are used everywhere when we need to check that a file or string of bits matches what we expect. For example VLC player uses hash to look for subtitles to the movie you are playing. Linux uses hash to check that the password you have entered matches the password hash that is stored in the hard drive. This ensures that if someone hacks into the computer, and obtains the passwords file, there is no function that can obtain the original password from the hash, since hash is only one way, but at the same time it’s trivial for the operating system to verify if the password you have entered is correct (since it will produce the same hash as the one stored in the hard drive).
Hash is a key piece of the blockchain algorithm. Since I intend to disect the blockchain algorithm to explain it piece by piece, it’s important that the basic pieces are well understood.